Every company today depends on digital systems to operate smoothly, from email and payment processing to customer databases and internal platforms.
When something goes wrong, the impact can spread fast and cause financial loss, downtime, damage to reputation, and even healthcare.
The risk becomes much greater as an organization grows because it must manage thousands of users, multiple locations, cloud services, remote access, and external partners at the same time.
Small businesses face threats too, but large enterprises deal with a wider attack surface and far more complex systems.
This is where enterprise cybersecurity comes into focus, as it brings together strategy, technology, and processes to protect large-scale environments.
In this blog, you will learn what it really means, how it is implemented inside organizations, and how companies apply it in real-world situations.
What is Enterprise Cybersecurity?
Enterprise cybersecurity is the framework of strategies, tools, and policies used to protect large organizations from digital threats.
It is designed for environments that operate at scale, where thousands of users, systems, and applications interact every day.
Regular IT security often focuses on basic protection, such as antivirus software and simple firewalls for smaller setups.
Its scope extends across internal networks, cloud services, employee devices, sensitive data, user identities, and third-party access from vendors or partners.
The goals are to protect valuable data, prevent attacks before they cause damage, reduce operational downtime, and maintain trust among customers, employees, and business stakeholders.
Core Components of Enterprise Cybersecurity
Large organizations rely on multiple security layers that work together to protect systems, users, and data across complex digital environments.
1. Network Security
Network security focuses on protecting the organization’s internal and external networks, communication channels, and connected systems from unauthorized access and attacks.
It includes firewalls, intrusion detection systems, and traffic-monitoring tools that filter and inspect data as it moves across the network.
By controlling how information flows between devices, offices, and cloud platforms, network security helps prevent the spread of malware, data breaches, and unauthorized access to critical systems.
2. Identity and Access Management (IAM)
Identity and access management controls who can access specific systems, applications, and data within the organization, ensuring that permissions are properly assigned and monitored.
It ensures that employees, contractors, and partners only have access to what they need for their specific job roles.
Tools such as multi-factor authentication, single sign-on, and role-based access controls reduce the risk of stolen credentials and insider misuse while improving visibility over user activity.
3. Data Protection and Encryption
Data protection focuses on securing sensitive information, whether it is stored in databases, processed by applications, or transmitted across internal and external networks.
Encryption converts data into unreadable code so that even if it is intercepted, it cannot be used without the correct key.
Additional measures, such as data loss prevention tools and backup systems, help prevent unauthorized sharing, accidental leaks, and permanent loss of important business information.
4. Endpoint Security
Endpoint security protects devices such as laptops, desktops, mobile phones, and servers that connect to the organization’s network.
Since these devices are common entry points for attacks, security software monitors them for malware, suspicious behavior, and unauthorized changes.
Centralized management allows security teams to update policies, deploy patches, and respond quickly if a device is compromised.
5. Cloud Security
Cloud security addresses risks across SaaS, IaaS, and PaaS environments where responsibilities are shared between providers and customers.
Under the shared responsibility model, providers secure physical infrastructure while organizations manage data, user access, configurations, and workloads.
Strong identity controls, encryption, logging, and continuous monitoring help maintain visibility and protection across the enterprise’s cloud platforms.
Why Large Organizations Need Enterprise-Level Protection?
Large organizations face a higher risk because their digital footprint is much wider.
A bigger attack surface means more servers, applications, cloud platforms, and connected systems that can be targeted.
At the same time, thousands of employees, contractors, and remote workers create countless access points, increasing the risk of credential misuse or human error.
These companies also store highly sensitive data, including customer records, financial information, and intellectual property.
A single breach can lead to financial loss and long-term reputation damage.
On top of that, regulatory and compliance requirements add further pressure, as organizations must comply with strict data protection laws and industry standards to avoid penalties and legal issues.
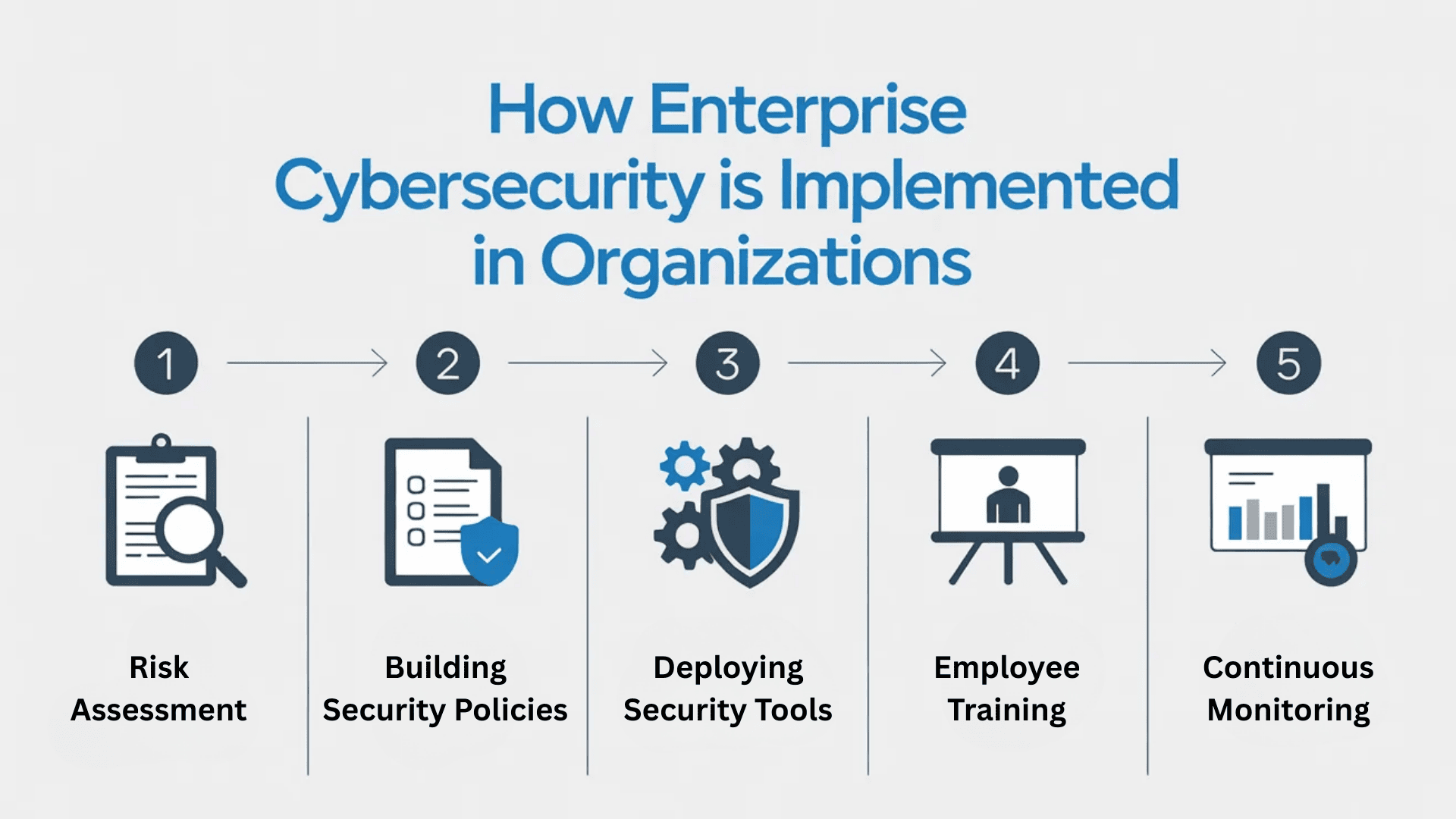
How is Enterprise Cybersecurity Implemented in Organizations?
Implementing enterprise cybersecurity requires a structured approach that combines planning, technology deployment, and continuous oversight across the entire organization.
Step 1: Risk Assessment and Security Audit
The process begins with identifying potential risks, vulnerabilities, and security gaps within the organization’s systems, infrastructure, and operational workflows.
A detailed security audit reviews networks, applications, user access, and data storage practices. Security teams analyze past incidents, test defenses, and evaluate compliance requirements.
This step helps organizations understand where they are most exposed and prioritize actions based on the level of risk and potential impact.
Step 2: Building Security Policies
After assessing risks, organizations create clear security policies that define acceptable use, access controls, data handling, and incident response procedures.
These policies set expectations for employees and third-party vendors while aligning with legal and industry requirements.
Well-defined guidelines help maintain consistency across departments and ensure that security practices are followed throughout daily operations.
Step 3: Deploying Security Tools and Systems
Once policies are established, technical controls are implemented to enforce them.
This includes firewalls, endpoint protection software, identity management systems, encryption tools, and monitoring platforms.
Integration across systems is important so that security teams can manage threats efficiently from a centralized dashboard with better visibility and control.
Proper configuration, timely patching, and regular updates ensure that these tools remain effective against evolving risks and newly emerging attack methods.
Step 4: Employee Training and Awareness
Technology alone cannot prevent every threat or security incident, so employee awareness and responsible behavior play a major role.
Organizations conduct training sessions to educate staff about phishing, password hygiene, safe browsing habits, and reporting suspicious activity.
Regular simulations and updates keep security top of mind. When employees understand their responsibilities, the likelihood of human error and accidental breaches decreases significantly.
Step 5: Continuous Monitoring and Improvement
Security implementation does not end after tools are deployed. Continuous monitoring helps detect unusual behavior, attempted breaches, and system vulnerabilities in real time.
Security teams review alerts, analyze trends and patterns, and update controls as new threats and vulnerabilities emerge.
Regular testing, audits, and policy revisions ensure that the security posture adapts to changes in technology, workforce, and risk landscape.
Common Challenges Organizations Face
Even with strong planning and tools in place, organizations face persistent issues that complicate security management in large, complex environments.
- Legacy systems: Outdated infrastructure lacks modern defenses, creating vulnerabilities that are difficult and costly to fix.
- Budget allocation: Limited budgets force leadership to balance security investments with other operational and growth priorities.
- Human error: Employee mistakes, such as weak passwords or phishing clicks, remain a frequent cause of breaches.
- Managing a remote workforce: Remote access from various devices and networks reduces visibility and increases security gaps.
- Keeping up with evolving threats: Attack methods constantly change, requiring continuous updates, monitoring, and strategy adjustments.
Real-World Examples of Enterprise Cybersecurity in Action
Large enterprises apply security strategies in practical ways to reduce risk, protect data, and maintain business continuity across complex global operations.
1. Microsoft and Multi-Factor Authentication
Microsoft enforces multi-factor authentication across its internal systems, cloud platforms, and administrative accounts.
Employees must verify their identity using additional authentication methods beyond passwords, such as authenticator apps, hardware tokens, or biometric verification.
This layered verification process significantly reduces the risk of account compromise caused by phishing, credential theft, or brute force attacks.
2. IBM and Security Operations Centers
IBM operates multiple global security operations centers that monitor enterprise networks, cloud environments, and client systems around the clock.
These centers collect data from security tools, analyze threat intelligence feeds, and review alerts generated by monitoring platforms in real time.
By combining automated detection technologies with experienced security analysts, IBM can quickly identify suspicious behavior, investigate incidents, and isolate compromised systems.
3. JPMorgan Chase and Data Encryption
JPMorgan Chase uses advanced encryption methods to secure customer data both in storage and during digital transactions across its banking platforms.
Sensitive financial information is encrypted across internal databases, mobile banking systems, and communication channels to prevent unauthorized access.
This ensures that even if data is intercepted during transmission, it cannot be read without authorized decryption keys.
4. Google and Zero Trust Security
Google applies a zero-trust security model across its enterprise environment, where no user or device is automatically trusted.
Every access request is verified based on identity, device health, and context, regardless of location. This approach reduces reliance on traditional perimeter defenses and strengthens internal access control.
By continuously validating users and devices, Google limits lateral movement and minimizes the impact of compromised credentials.
5. Amazon Web Services and Cloud Security Controls
Amazon Web Services applies multiple layers of cloud security controls across its global infrastructure, covering data centers, networks, and platform services.
Using identity policies, encryption services, logging tools, and configuration monitoring, AWS protects its environment and customer workloads under the shared responsibility model.
Continuous monitoring and automated alerts detect misconfigurations and suspicious activity early, improving visibility and overall protection across cloud environments.
The Future of Enterprise Cybersecurity
The future of enterprise cybersecurity is shaped by smarter technology and shifting infrastructure models.
AI-driven threat detection is becoming more advanced, allowing systems to identify unusual behavior, predict attack patterns, and reduce false alerts.
At the same time, ransomware is also upgrading, finding different ways to attack while remaining unidentified.
Instead of reacting only to known threats, organizations can detect suspicious activity earlier through behavior analysis.
Automation in response systems is also gaining traction. Automated workflows can isolate devices, disable accounts, and block malicious traffic within seconds.
There is also a stronger focus on identity security, with tighter access controls and continuous user verification becoming central to defense strategies.
Conclusion
Enterprise cybersecurity is the structured framework organizations use to secure large-scale digital environments that include networks, cloud platforms, endpoints, user identities, and sensitive data.
Throughout this blog, we covered what it means, why enterprises require stronger protection than smaller businesses, and the core components that form its foundation.
From risk assessments and policy building to deploying tools, training employees, and continuously monitoring systems, every layer plays a defined role in reducing exposure and limiting operational disruption.
As technology advances and attack methods become more sophisticated, organizations must continuously refine their defenses, strengthen identity controls, and improve visibility across cloud and on-premises systems.
Is your organization prepared to strengthen its security posture for the challenges ahead? Share your insights or questions in the comments below.