Data flows through every part of modern business, quietly powering decisions, customer experiences, and daily operations.
Yet beneath that convenience often lies uncertainty about where sensitive information truly resides and how well it is protected.
Many organizations reach a point of realization when they find that valuable data is scattered across cloud platforms, shared drives, and third-party tools without clear oversight.
Without clear visibility, even strong security investments can leave gaps unnoticed. Businesses expanding into the cloud frequently pause to evaluate: what is DSPM, and its real value.
Data Security Posture Management speaks to organizations that want confidence instead of guesswork, clarity instead of blind spots.
This blog clearly explains DSPM’s meaning, how it works in modern environments, and the best practices for successful implementation.
What is DSPM & How Does it Work?
DSPM stands for Data Security Posture Management, which is a way for organizations to find, assess, and protect sensitive information across cloud and hybrid environments.
The term gained wider recognition after Gartner introduced DSPM in 2022, highlighting the growing need for a data-focused security approach.
According to IBM, DSPM helps teams see where their data lives, how risky it might be, and where exposures exist so they can act faster and smarter.
The focus of DSPM is on data itself rather than just on servers, networks, or devices.
It looks at sensitivity, access rights, and how data moves. Modern cybersecurity demands this shift because data now lives everywhere.
DSPM works by continuously discovering data, tagging its sensitivity, analyzing access paths, and alerting on risks.
It provides insight into data risk and enables faster fixes to prevent unauthorized exposure.
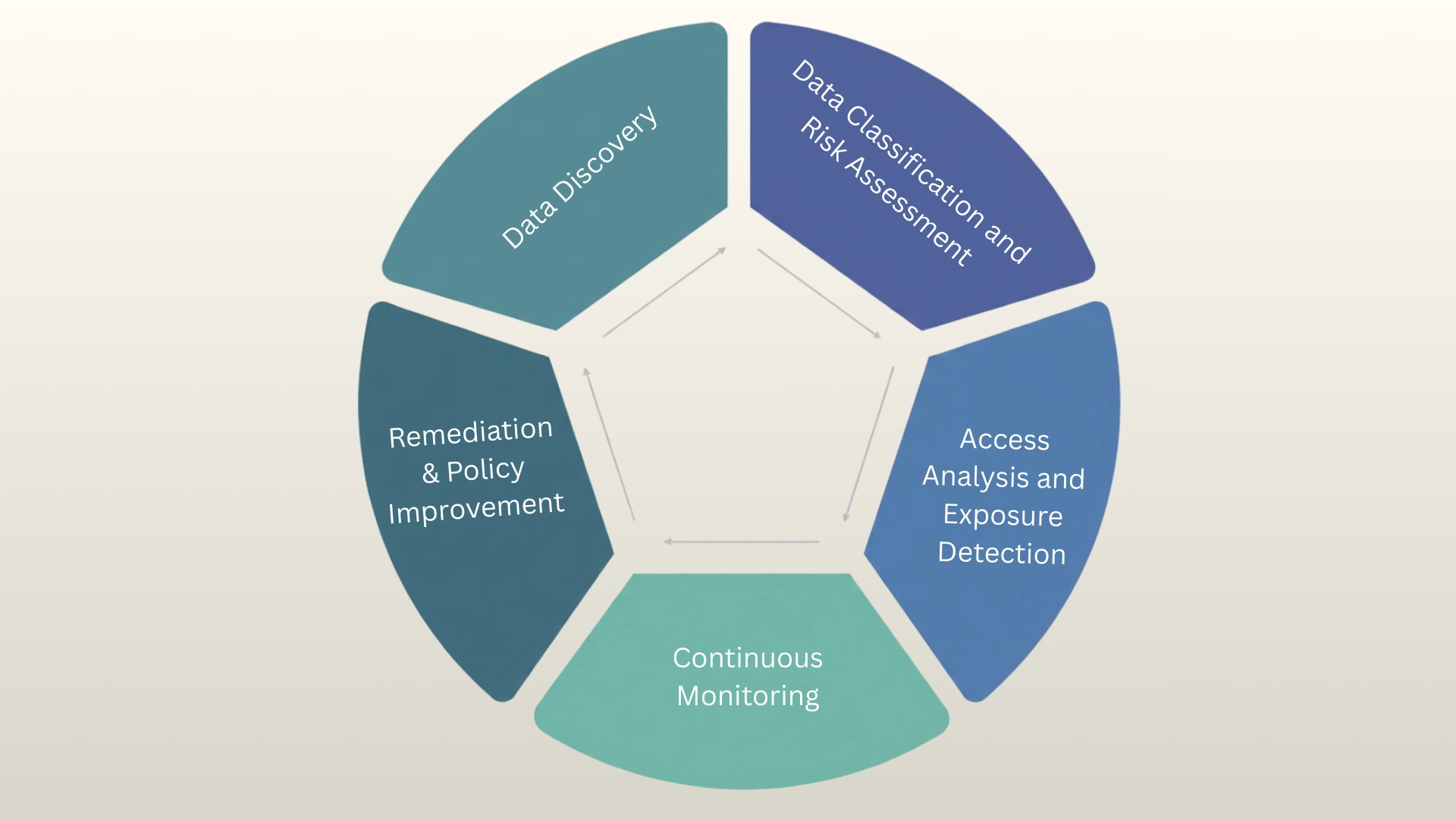
What are the Stages of The DSPM Lifecycle?
Data Security Posture Management follows a structured lifecycle that helps organizations continuously protect sensitive information across complex environments.
1. Data Discovery
The first stage of the DSPM lifecycle focuses on discovering and mapping all data across cloud, hybrid, and on-premise systems.
According to Cloud Security Alliance, DSPM tools provide visibility into the inventory of sensitive data across cloud services like databases, object storage, and managed platforms.
It also helps uncover shadow data, which refers to unknown, forgotten, or unmanaged data stored outside approved systems without proper oversight.
DSPM tools automatically scan databases, storage buckets, SaaS applications, and file systems to create a complete inventory.
2. Data Classification and Risk Assessment
After identifying the data, the next step is to classify it by sensitivity and business impact.
DSPM tools analyze content to determine when it contains personal data, financial records, health information, or intellectual property.
Many platforms now use ML-based contextual classification, which applies machine learning models to understand context within datasets rather than relying only on keyword matching.
Risk assessment also examines access permissions and potential exposure points.
3. Access Analysis and Exposure Detection
This stage evaluates who can access sensitive data and whether that access is appropriate.
Over-permissioned accounts and misconfigured settings often create unnecessary risk. DSPM continuously monitors user roles, service accounts, and third-party access.
It identifies excessive privileges, public exposures, and weak access controls.
Many data breaches happen because access rights were never properly reviewed. By analyzing permissions and exposure paths, DSPM helps reduce insider threats.
4. Continuous Monitoring
Data environments constantly change as new files are created and permissions are updated.
Continuous monitoring ensures that security posture remains accurate over time. DSPM tools track changes in data location, sensitivity, and access levels.
When new risks appear, automated alerts notify security teams immediately.
This prevents issues from remaining hidden for long periods, and monitoring is not limited to scheduled scans.
5. Remediation & Policy Improvement
The final stage focuses on fixing identified risks and strengthening long-term policies.
DSPM solutions often provide guided remediation steps or automated corrections. These may include tightening permissions, encrypting exposed data, or updating security policies.
After remediation, teams review patterns to improve governance practices.
Lessons learned during risk detection help refine access rules and compliance strategies. This stage closes the loop in the lifecycle.
What is DSPM for AI?
Data Security Posture Management for AI refers to applying DSPM practices specifically to protect data used, generated, or processed by artificial intelligence and machine learning systems.
As AI models train on large datasets from multiple sources, sensitive information can be at greater risk of exposure, misuse, or leakage if not properly managed.
This includes specific AI data types such as training datasets, labeled images, chat transcripts, prompt inputs, model outputs, embeddings, synthetic data, and fine-tuning datasets.
This approach ensures that AI systems have only access to appropriate data and that training and output processes comply with data privacy rules.
It supports safer and more secure AI development and deployment.
It works by mapping data flows, enforcing least-privilege access policies, and ensuring compliance with regulations.
Common DSPM Use Cases Across Industries
Organizations across industries use DSPM to gain better visibility and control over sensitive information. DSPM supports multiple business functions, from compliance to threat detection.
- Cloud Data Protection: DSPM helps organizations identify sensitive data stored in cloud platforms such as AWS, Azure, and Google Cloud.
- Regulatory Compliance Support: Companies use DSPM to meet requirements under regulations such as HIPAA, GDPR, and CCPA.
- Insider Threat Detection: This helps security teams detect risky behavior from employees, contractors, or compromised accounts before damage occurs.
- Data Risk Prioritization: By combining sensitivity levels with exposure insights, DSPM allows organizations to focus remediation efforts.
- Mergers and Acquisitions Security Reviews: During acquisitions, DSPM helps assess the security posture of newly integrated systems.
Challenges & Limitations of DSPM
While DSPM provides strong visibility and risk control, it is not without challenges. Organizations often face technical, operational, and strategic hurdles during implementation.
- Complex Data Environments: Managing structured and unstructured data across multi-cloud systems significantly increases discovery complexity.
- Integration Difficulties: Connecting DSPM tools with existing security stacks may require time, customization, and expertise.
- Resource and Skill Gaps: Effective DSPM management requires trained security teams with knowledge of cloud and data governance.
- False Positives and Alert Fatigue: Excessive alerts can overwhelm teams and reduce response efficiency if not properly tuned.
- Scalability Concerns: Rapid data growth may strain DSPM performance without proper infrastructure planning and optimization.
DSPM vs DLP vs CSPM
DSPM, DLP, and CSPM are often grouped together, but they solve different problems. Understanding it helps organizations choose the right solution based on their security priorities.
| Feature | DSPM (Data Security Posture Management) | DLP (Data Loss Prevention) | CSPM (Cloud Security Posture Management) |
|---|---|---|---|
| Primary Focus | Identifies sensitive data and reduces exposure risks across environments. | Prevents unauthorized sharing or leakage of sensitive information. | Detects and fixes cloud configuration weaknesses. |
| Security Approach | Data-centric model prioritizing sensitivity, access. | Content inspection model monitoring data in motion and use. | An infrastructure-centric model focused on cloud resource settings. |
| Environment Coverage | Covers multi-cloud, SaaS, hybrid, and on-premises systems. | Monitors endpoints, networks, email systems, and cloud apps. | Focuses mainly on public cloud platforms like AWS and Azure. |
| Main Goal | Strengthen overall data security posture and visibility. | Stop sensitive data from leaving secure environments. | Ensure cloud services follow security best practices. |
Best Practices for DSPM Implementation
Implementing DSPM requires more than simply deploying a tool. Organizations need a structured plan that aligns data visibility, governance policies, and security operations.
- Start with Complete Data Discovery: Ensure all structured and unstructured data sources are identified before enforcing security controls.
- Align DSPM with Data Governance Policies: Integrate classification standards, retention rules, and compliance requirements into the DSPM framework.
- Integrate with Existing Security Tools: Connect DSPM with SIEM, IAM, and cloud security platforms for unified visibility.
- Prioritize Risk Based on Data Sensitivity: Focus remediation efforts on highly sensitive and widely accessible data assets first.
- Enable Continuous Monitoring and Automation: Use automated alerts and remediation workflows to maintain a consistent security posture.
Conclusion
Data security is no longer limited to protecting networks or devices.
Understanding what DSPM is helps organizations shift their focus directly to their most valuable asset: data itself.
The DSPM meaning centers on continuous visibility, risk assessment, and protection of sensitive information across cloud and hybrid environments.
Data Security Posture Management allows teams to find hidden data, classify it by sensitivity, monitor access, and reduce exposure before incidents occur.
This approach strengthens compliance efforts, improves risk prioritization, and supports smarter security decisions.
As data volumes continue to grow, organizations must evaluate if they truly understand where their critical information resides and who can access it.
What are your thoughts on DSPM? Share your opinions or insights in the comments below.